In a recent cyber assault that has sent shockwaves through the U.S. aerospace sector, a sophisticated spearphishing attack orchestrated by the threat actor AeroBlade has revealed alarming vulnerabilities. This incident underscores the pressing need for enhanced cybersecurity measures in critical infrastructure industries, especially within aerospace, to counter evolving threats.
Lessons Unlearned in Critical Industries
Roger Grimes, a data-driven defense evangelist at KnowBe4, underscores the necessity of four crucial steps to thwart such attacks: anti-social engineering training, consistent patching, phishing-resistant multifactor authentication, and robust password policies. Grimes asserts, “If the aerospace industry took just those four steps, threats such as AeroBlade would not see continued success.” This breach highlights the significance of proactive cybersecurity measures for safeguarding critical industries against persistent threats.
Unraveling the AeroBlade Spearphishing Attack
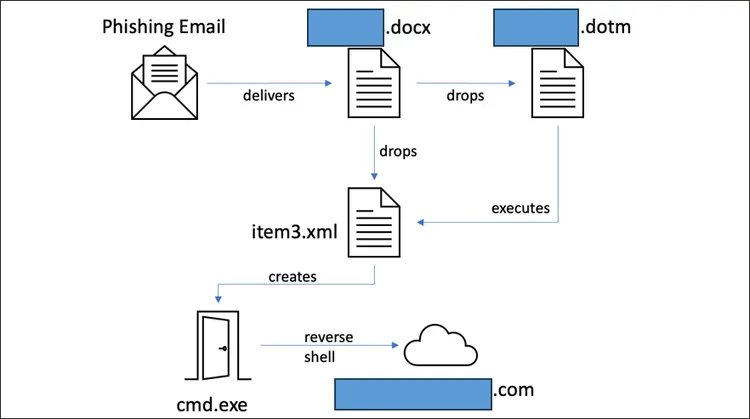
The BlackBerry Threat Research and Intelligence team dissected the attack, revealing that AeroBlade’s spearphishing strategy involved a weaponized document named [redacted].docx, utilizing a remote template injection technique and malicious VBA macro code. Operational since September 2022, the attack entered the offensive phase in July 2023, showcasing a sophisticated and strategically planned assault uncommon in typical cyberattacks.
The Sophistication Behind the Spearphishing Campaign
Callie Guenther, senior manager of cyber threat research at Critical Start, emphasized the attack’s sophistication. The year-long gap and the use of a remote template injection technique indicated a high level of commitment, suggesting involvement from state-sponsored or highly organized criminal groups. Guenther explained that this technique cleverly bypassed security measures, granting the attacker control over the victim’s system and exhibiting meticulous reconnaissance capabilities.
The Patient Adversary: Understanding the Threat Actor
Donovan Tindill, director of OT cybersecurity at DeNexus, noted the threat actor’s patience, spending nine months in a testing phase before escalating the offensive attack. While BlackBerry expresses “high confidence” in identifying commercial cyber espionage, Tindill warns that there’s no guarantee the threat actor won’t escalate to ransomware or data encryption in the future. Anurag Gurtu, CPO at StrikeReady, stressed the seriousness of the AeroBlade attack due to the sensitive nature of aerospace company data, urging organizations to strengthen cybersecurity defenses and prioritize employee training.
Strengthening Defenses for Future Resilience
The AeroBlade spearphishing attack serves as a stark reminder of the evolving and sophisticated nature of cyber threats targeting critical industries. As the aerospace sector faces increasing risks, adopting comprehensive cybersecurity measures and investing in employee training are imperative to mitigate potential breaches and safeguard sensitive information. Organizations must remain vigilant and proactive to ensure the resilience of their defenses against ever-evolving cyber threats.
Related Articles
Hackers Compromise ISPs with Malware to Steal Customer Credentials
A critical zero-day vulnerability exploited since June that affected ISPs has now been patched. Malicious hackers, likely operating on behalf of the Chinese government, have been leveraging a high-severity zero-day vulnerability to infect at least four U.S.-based ISPs...
Microsoft Ends Support for Windows 10: How to Prepare for the Transition to Windows 11
As technology rapidly evolves, so do the operating systems that power our devices. Microsoft has announced that it will officially end support for Windows 10 on October 14, 2025. This decision marks a significant milestone for the millions of users who rely on Windows...
Cyberattack Disrupts Microchip Technology’s Manufacturing Operations
US semiconductor leader Microchip Technology (NASDAQ: MCHP) has reported a cyberattack that has significantly impacted operations at several of its manufacturing facilities. On August 17, the company detected unusual activity within its IT systems, and by August 19,...

